DATASHEETS
Case Study: Finance
Supporting hundreds of downstream institutions means infrastructure failures can have far‑reaching consequences. Learn how this financial organization’s team evaluated ZeroLock’s hypervisor-level protection and deployed it with minimal operational overhead to reduce systemic risk.
Case Study: Healthcare
With strict uptime expectations for their EMR and a VMware-heavy environment, this security team at a rural healthcare provider prioritized the hypervisor as the missing layer in their defenses. Read how they validated the solution in a short evaluation and rolled protection into production under real-world pressure.
Protect
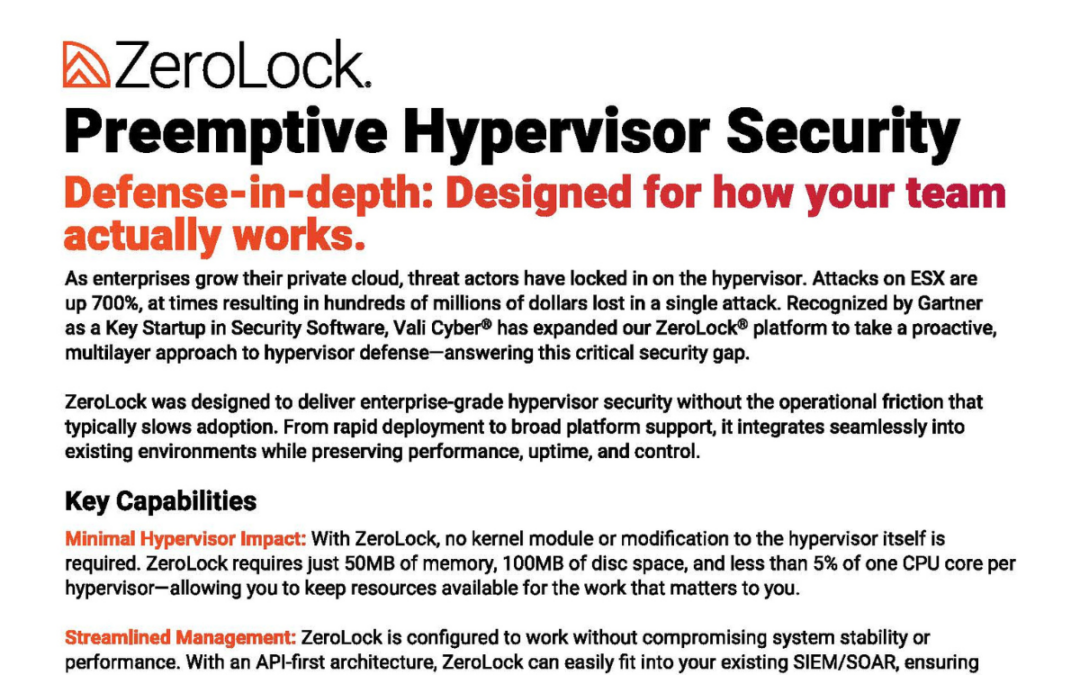
No security strategy is static, which is why resilience matters as much as prevention. With patented AI Detection and Automated Remediation, you gain the ability to detect and respond to threats in real time—limiting blast radius, accelerating recovery, and keeping the business running.
Prevent
ZeroLock leads with preventative best practices, going beyond traditional mandatory access control capabilities by offering features like easily configured and universally applied rules and policies that can be deployed across your hypervisor environment, helping you stop attacks before they even start.
Perform
ZeroLock was designed to deliver enterprise-grade hypervisor security without the operational friction that typically slows adoption. From rapid deployment to broad platform support, it integrates seamlessly into existing environments while preserving performance, uptime, and control.
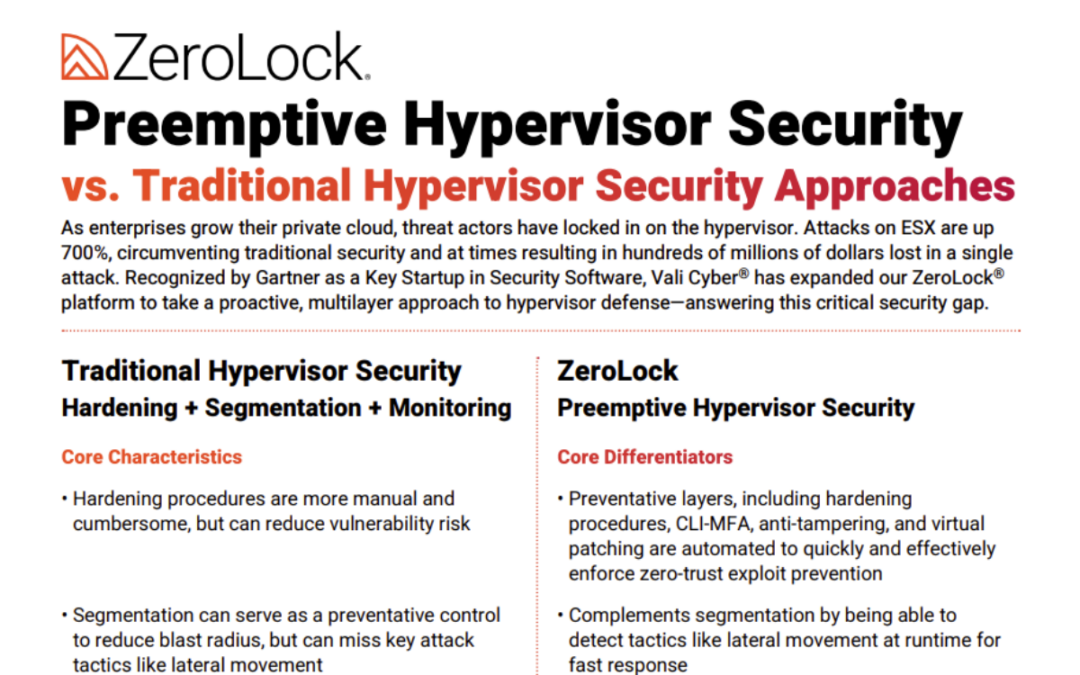
Preemptive Hypervisor Security vs. Traditional Hypervisor Security
Compare traditional hypervisor security with ZeroLock’s preemptive, Gartner‑recognized protection that stops ransomware in seconds.
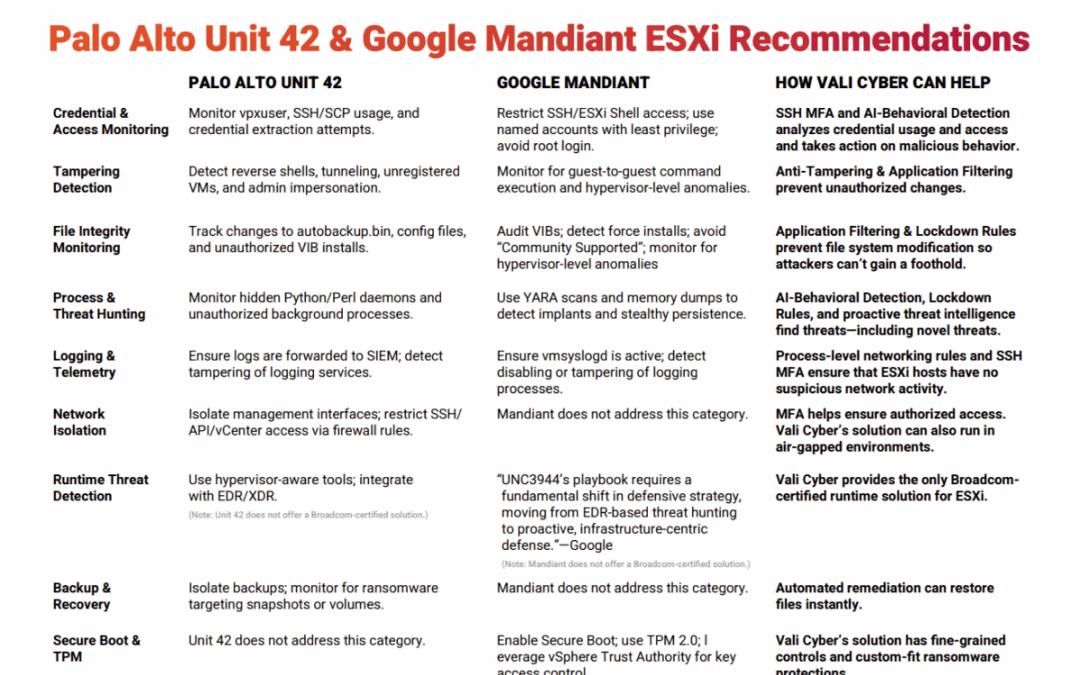
Palo Alto Unit 42 & Google Mandiant ESXi Recommendations
How does your Incident Response plan address ESXi? Check out these recommendations from Unit 42 & Mandiant, along with how ZeroLock can help!
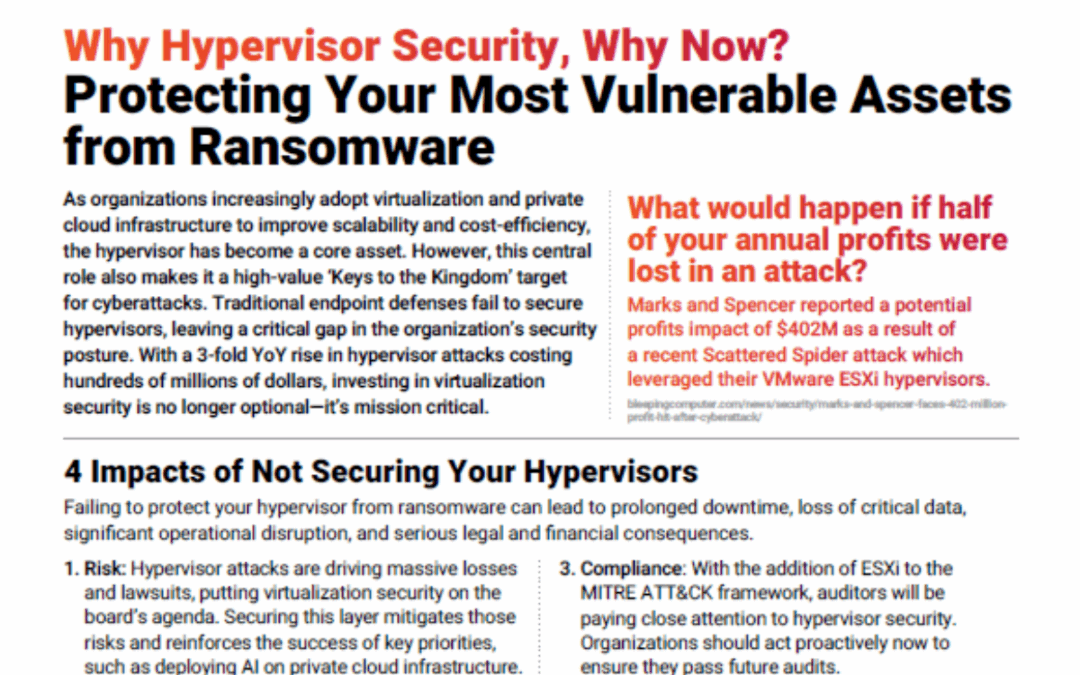
Protecting Your Most Vulnerable Assets from Ransomware
As organizations increasingly adopt virtualization and private cloud infrastructure to improve scalability and cost-efficiency, the hypervisor has become a core asset. However, this central role also makes it a high-value target for cyberattacks. Investing in virtualization security is no longer optional—it’s mission critical.
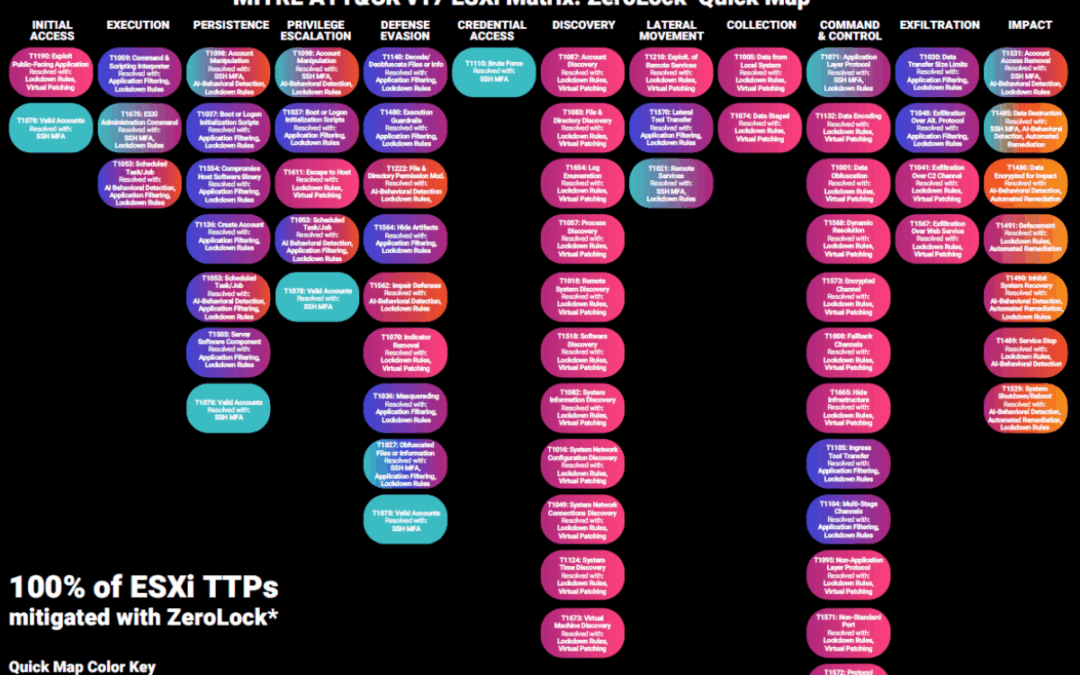
MITRE ATT&CK v17 – ZeroLock® Quick Map
Quickly scan this map to see how ZeroLock® mitigates 100% of MITRE ATT&CK v17 ESXi TTPs when properly configured and fully deployed featuring SSH MFA, Application Filtering, Lockdown Rules, AI Detection, and more!
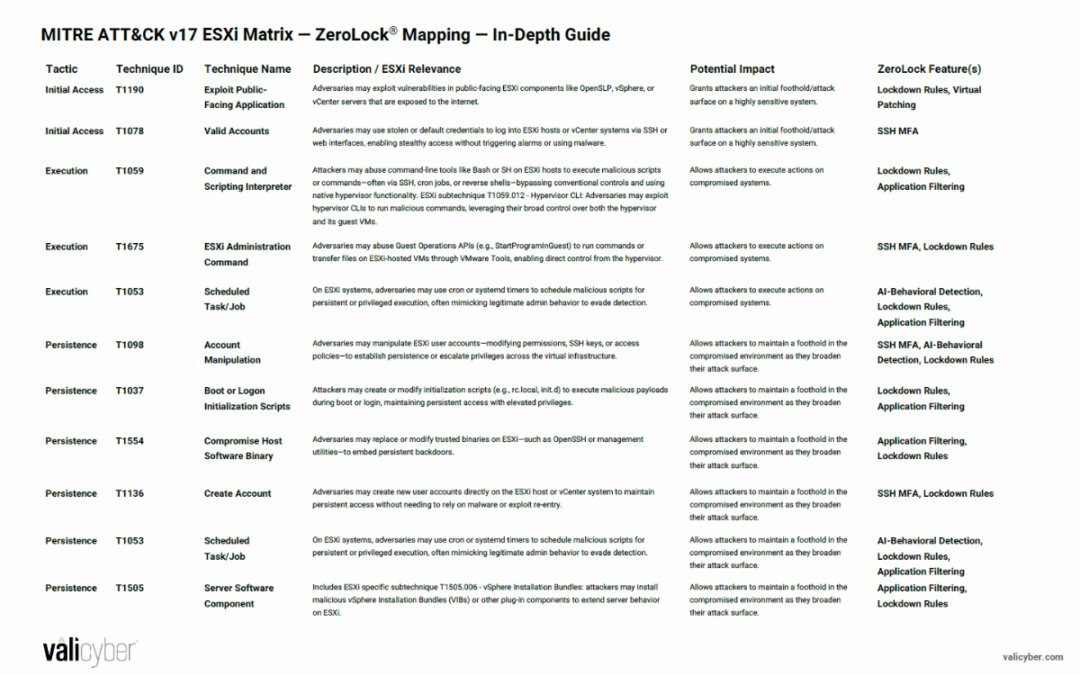
MITRE ATT&CK v17 ESXi Matrix — ZeroLock® Mapping — In-Depth Guide
Check out this in-depth guide to see how ZeroLock® mitigates 100% of MITRE ATT&CK v17 ESXi TTPs when properly configured and fully deployed featuring SSH MFA, Application Filtering, Lockdown Rules, AI Detection, and more!
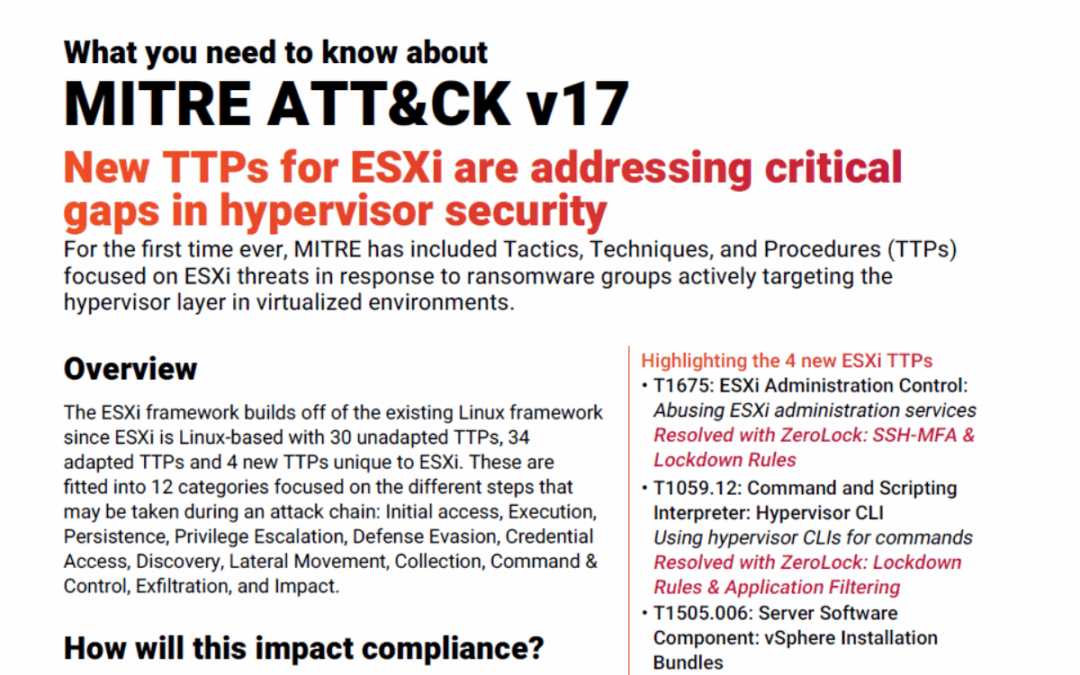
MITRE ATT&CK v17: New TTPs for ESXi
For the first time ever, MITRE has included Tactics, Techniques, and Procedures (TTPs) focused on ESXi threats in response to ransomware groups actively targeting the hypervisor layer in virtualized environments.
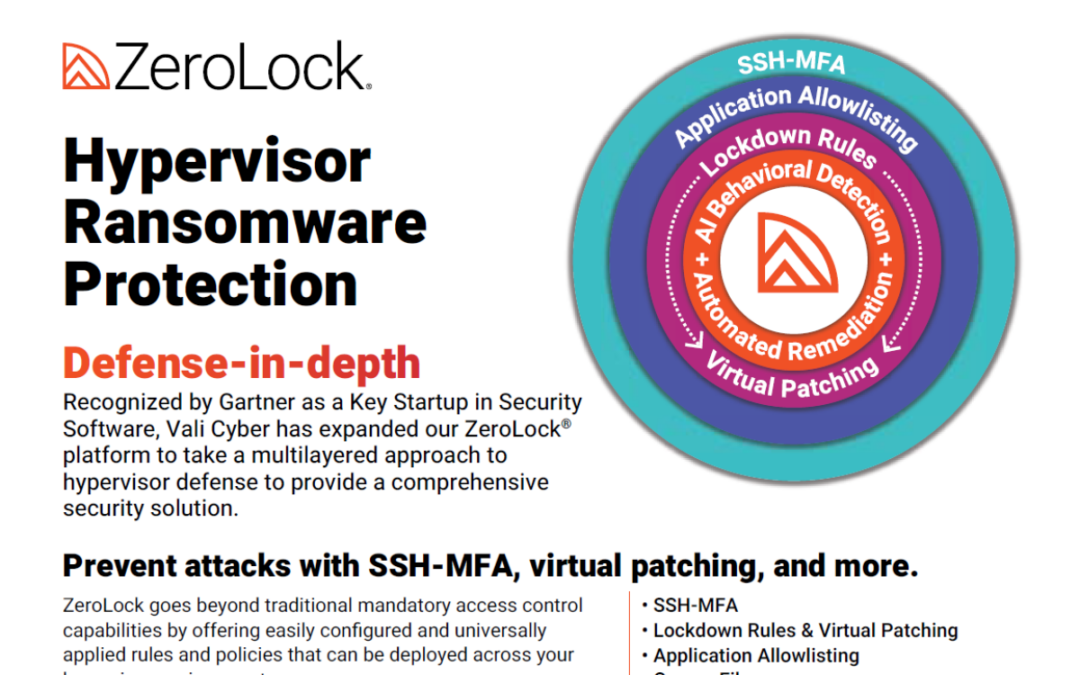
Hypervisor Ransomware Protection
ZeroLock® protects hypervisors from ESXi threats with advanced capabilities like SSH MFA, virtual patching, application filtering, AI-powered remediation, and more.
Virtual Patching
ZeroLock® virtual patching protects hypervisors from emerging ESXi vulnerabilities and the costly downtime associated with traditional patching.
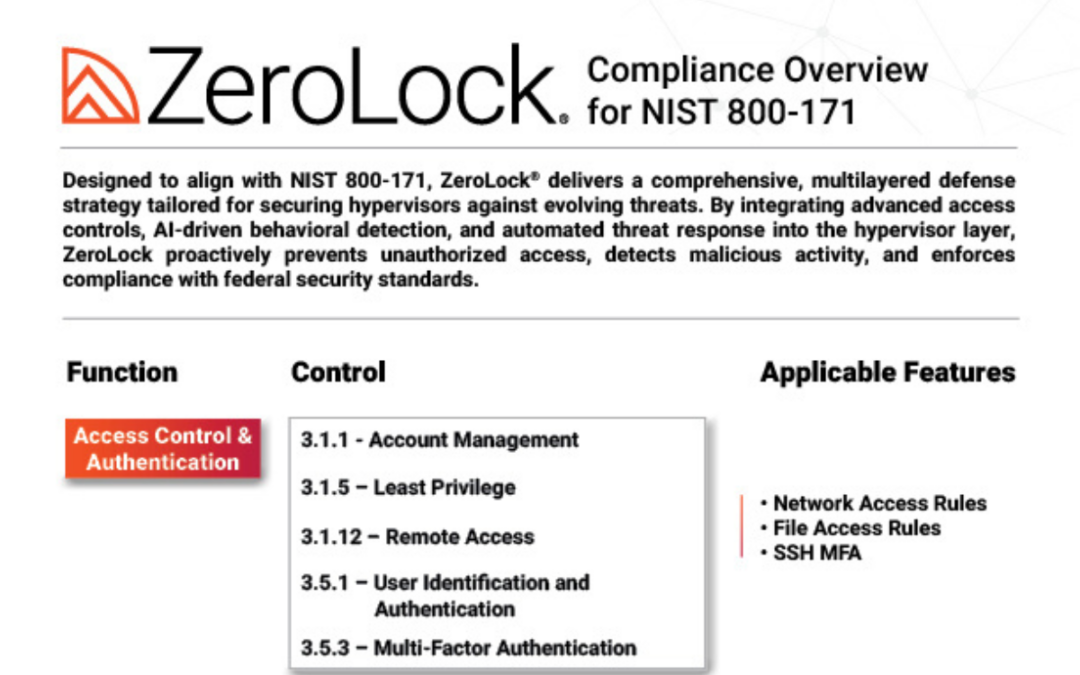
Compliance Overview for NIST 800-171
Designed to align with the controls of NIST 800-171, ZeroLock® delivers a comprehensive, multilayered defense strategy tailored for securing hypervisors against evolving threats.
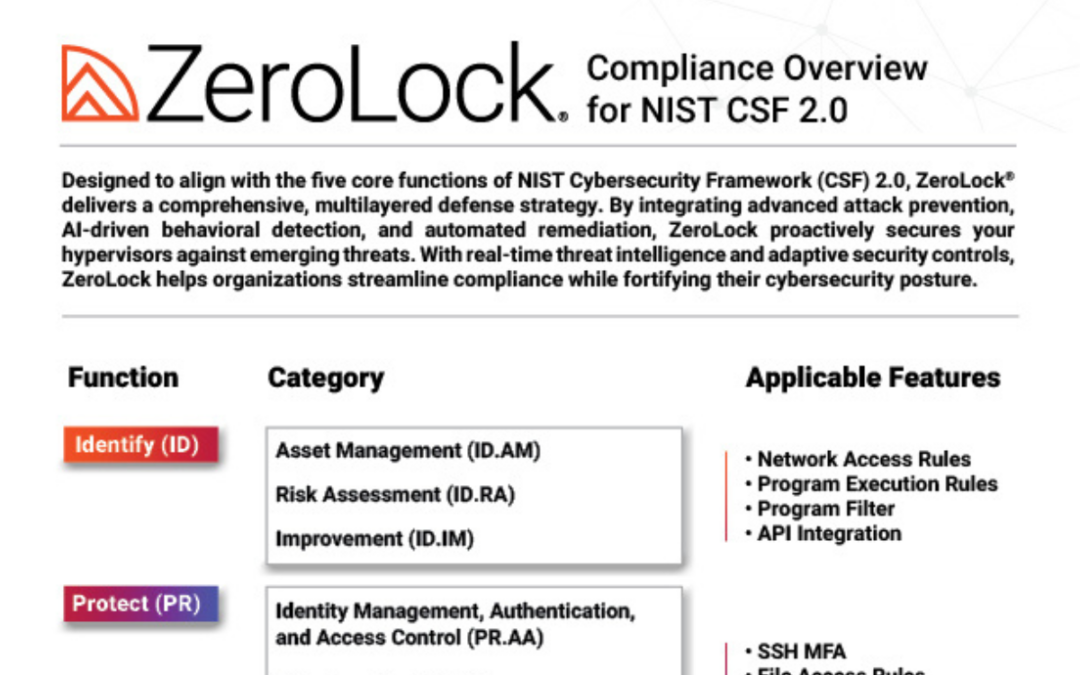
Compliance Overview for NIST CSF (Cybersecurity Framework) 2.0
Designed to align with the five core functions of NIST Cybersecurity Framework (CSF) 2.0, ZeroLock® delivers a comprehensive, multilayered defense strategy for hypervisors.
Manufacturing
ZeroLock® offers a multilayered approach to security by combining attack prevention with AI behavioral detection and automated remediation to secure manufacturing hypervisors, intellectual property, and confidential data.
