HYPERVISOR RANSOMWARE PROTECTION
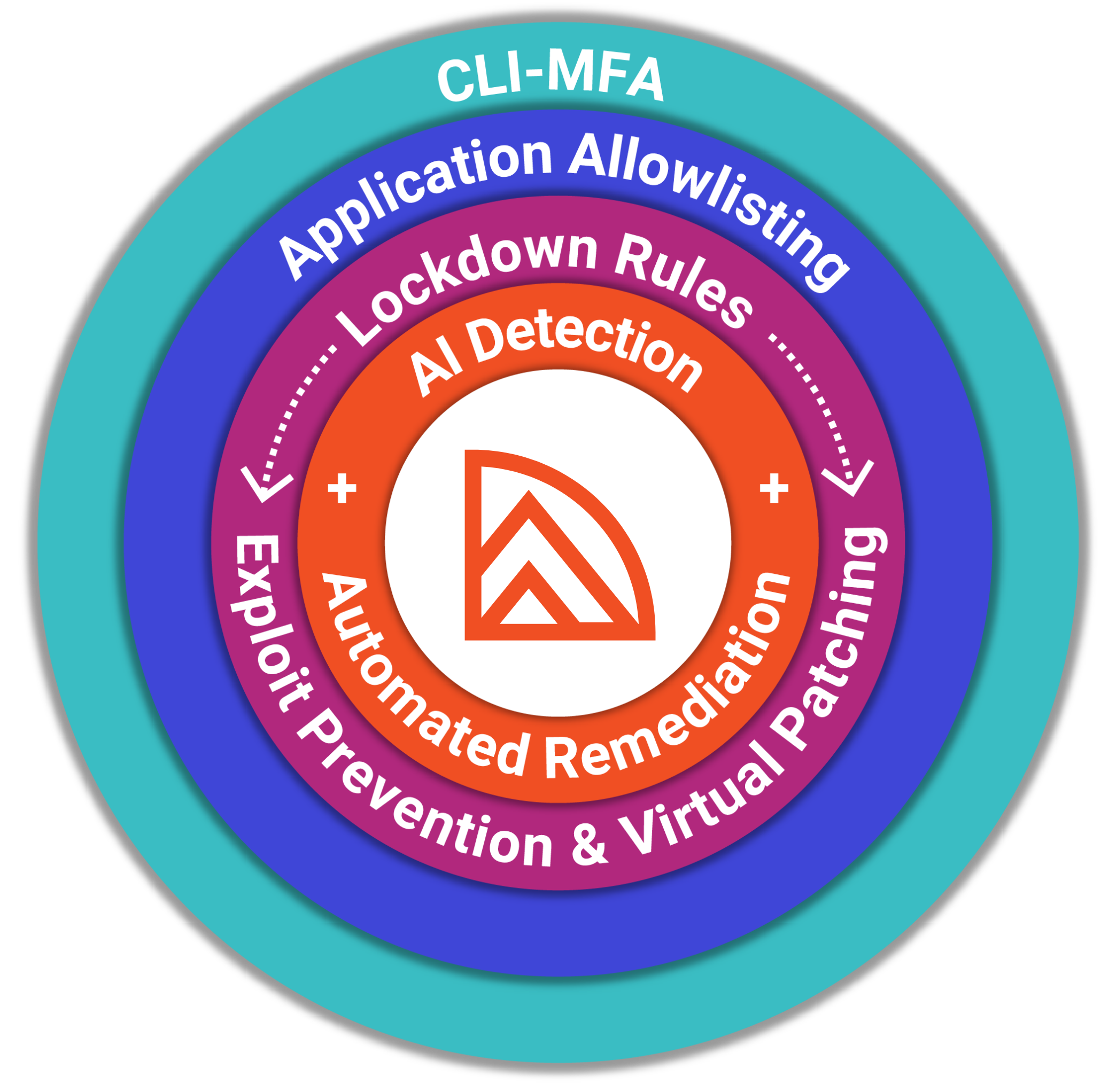
Prevent attacks with CLI-MFA, application filtering, and lockdown rules.
ZeroLock® goes beyond traditional mandatory access control capabilities by offering easily configured and universally applied rules and policies that can be deployed across your hypervisor environment.
ZeroLock’s® prevention capabilities include:
- CLI Multifactor Authentication (MFA)
- Application Filtering
- Process Behavior Controls
- Network Access Controls
- File Access Controls
- Canary Files
- Tamper Protection
ZeroLock’s® response capabilites include:
- Ransomware Protection
- Wiperware Protection
- Real-time Threat Remediation
- Automated File Rollback
- Attacker Persistence Removal
- Fully Automated Process Tree Creation
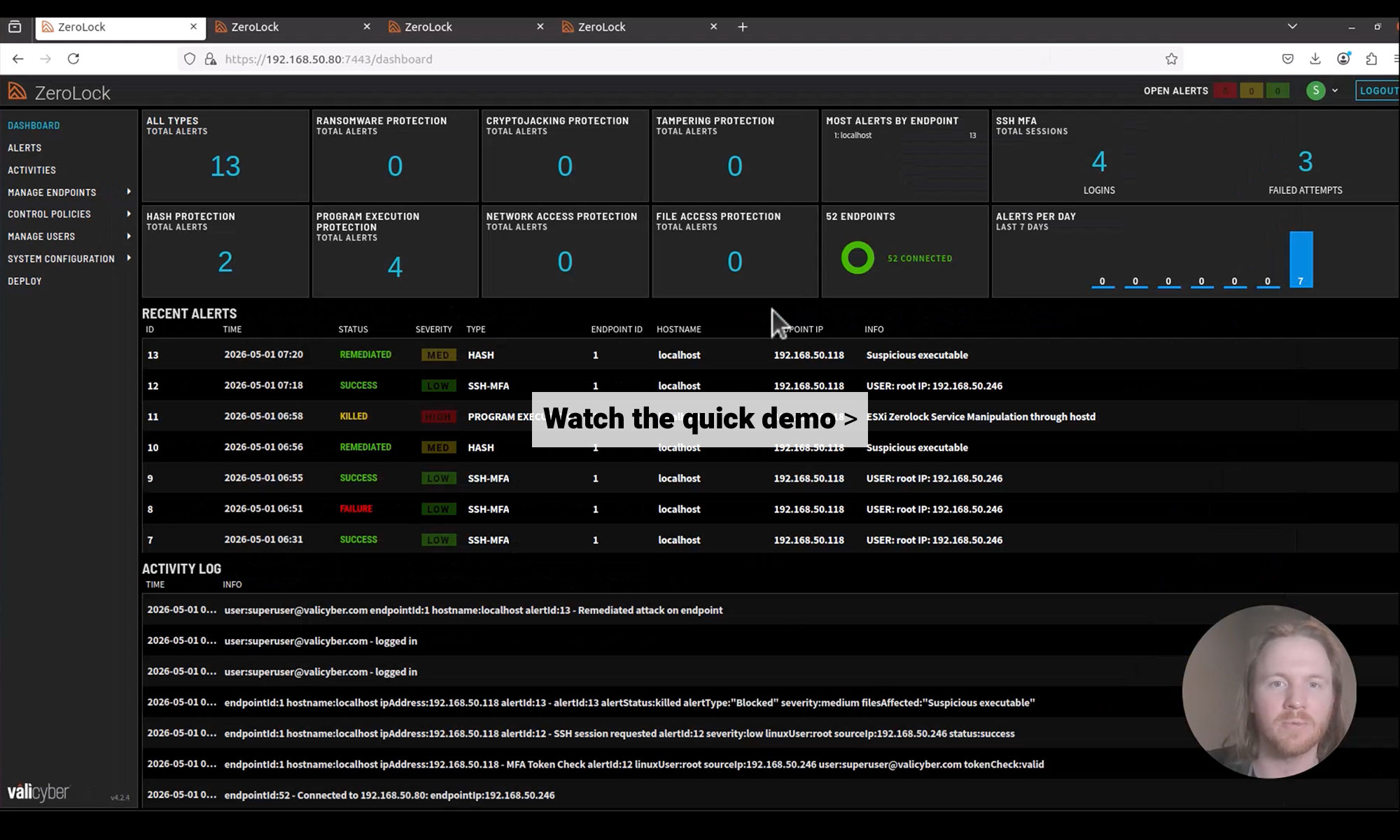
Ensure uptime with AI detection and automated remediation.
ZeroLock’s® AI detection identifies malware in real-time. Our proprietary algorithms detect and stop traditional and fileless ransomware attacks with >98% efficacy and offer the ability to automatically remediate file damage and remove attackers with no user intervention required—helping you to ensure zero downtime.
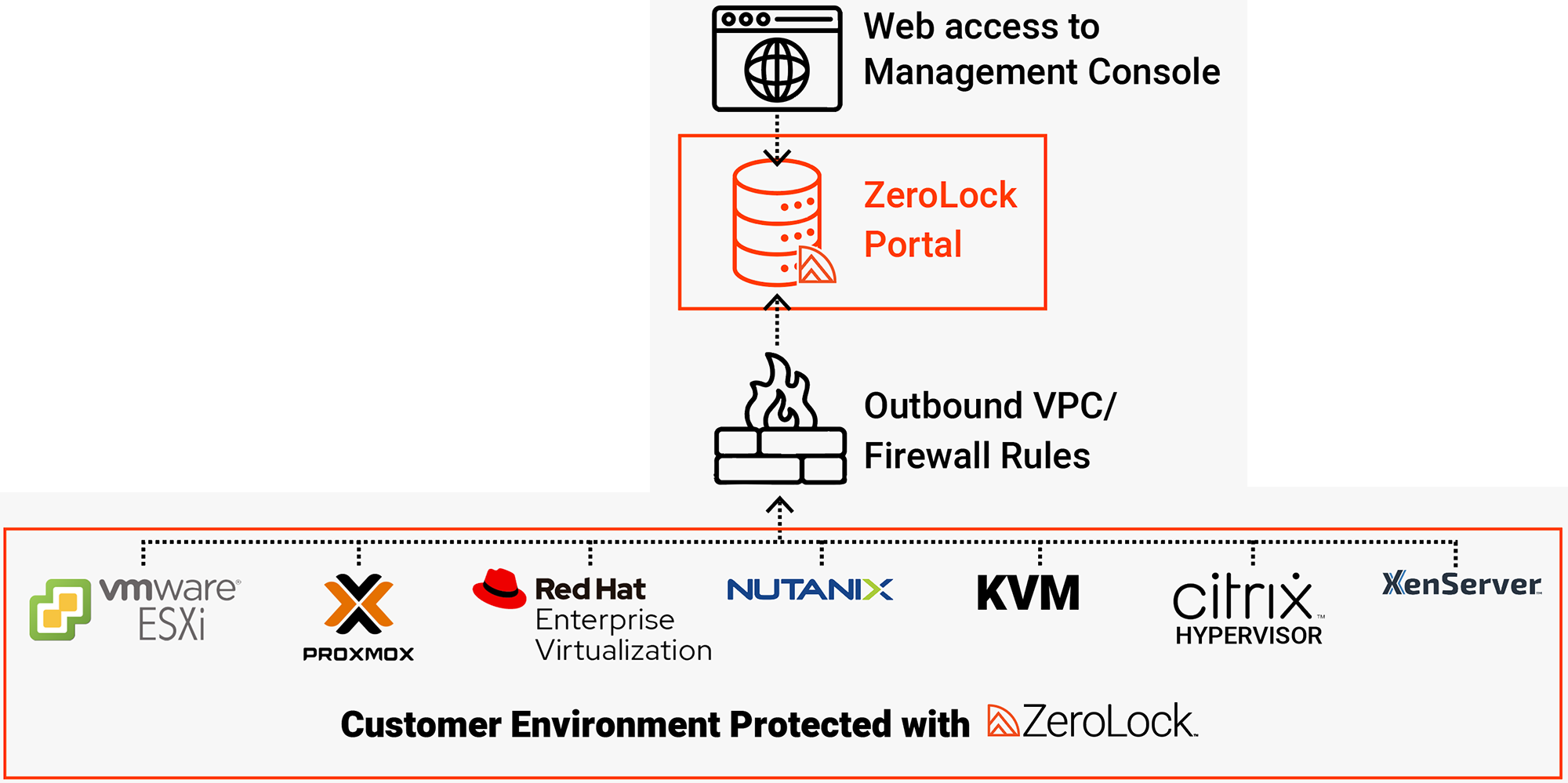
Deploy and manage flexibly.
With ZeroLock®, no modification to the hypervisor itself is required, and deployment is as simple as one line in the terminal, or through a partner portal like VCenter. ZeroLock® is configured to work while also maintaining system stability and performance.
ZeroLock’s® management capabilities include:
- Compatible with VMware ESXi, Nutanix, XenServer, Citrix Hypervisor, Proxmox, Red Hat Enterprise Virtualization (RHEV), and KVM
- API-based architecture
- Quick SIEM/SOAR integration using ZeroLock’s® syslog provider
- Single agent
- One-line deployment
- Minimal overhead (50MB RAM)
- Signed VIB & deployable via vCenter for ESXi
AdaptableDeploymentFramework
24-7 support every step of the way.
Operationalization is no small lift. Vali Cyber’s® support team is there for you every step of the way through deployment and continues to be available to answer questions any time of day as you manage ZeroLock® in your environment. We also schedule periodic check-ins to make sure you are getting the most out of your ZeroLock® purchase.

Learn more about hypervisor security.
TECH SPECS
ZeroLock® Endpoint Agent Requirements for Hypervisors
OS
- VMware Cloud Foundation 9.X
- VMware ESXi, 6.7+ (Older versions supported upon request.)
- Nutanix-managed ESXi, 6.7+
- Nutanix AHV 2017+*
- XenServer, 6.5+
- Citrix Hypervisor, 8.0+
- Proxmox, 3.0+
- Red Hat Enterprise Virtualization, 3.6+
- HPE Morpheus, 8.0+
- Dell VxRail, 4.8+
- KVM, Kernel 3.5+
* Note, Nutanix does not currently support third-party products running on AHV.
Processor
Memory
50MB
Disk Space
100MB
Kernel Mods.
No kernel modification or modules required
Installation Methods
- One-line, web-based deployment (Wget)
- File-based deployment (Tar.gz or Bash)
- VCF & ESXi: Signed VIB and deployable via vCenter
RAM
16GB
Disk Space
128GB (dependent on number of endpoints and data retention duration)
CPU Cores
6 or more recommended
Installation Reqs.
- Self-deployment: Latest version of Docker installed
- OVA-deployment: ESXi 7.0 or later
Documentation
Existing integrations
• SIEM: Splunk, Sumo Logic, Elastic
• SOAR: Swimlane
• Incident API: Veeam