IN THE NEWS

AI Is Moving Into Production Workflows, And So Are The Risks

Vali Cyber® Brings Hypervisor Visibility into the SOC with Google Security Operations
Security teams have spent years centralizing visibility across endpoints, identities, and networks. But one critical layer has remained largely invisible: the hypervisor.
Today, that changes. Vali Cyber’s ZeroLock® is enabling organizations to stream hypervisor security events directly into their existing SecOps workflows with Google Security Operations.
Closing a Critical Visibility Gap
Traditional SIEMs and detection tools were not designed to capture activity at the virtualization layer. As a result, security teams often lack visibility into one of the most critical parts of their infrastructure.
This is something that’s been previously highlighted by Google Mandiant. As part of their UNC3944 (Scattered Spider) analysis, Mandiant noted that these new playbooks require, “a fundamental shift in defensive strategy, moving from EDR-based threat hunting to proactive, infrastructure-centric defense” at the virtualization layer.
The integration brings ZeroLock’s hypervisor-level signals into Google Security Operations—reducing blind spots and extending detection coverage below the operating system.
Unified Visibility, No Disruption
ZeroLock integrates with Google Security Operations, allowing teams to:
- Centralize hypervisor activity alongside existing enterprise telemetry
- Correlate hypervisor events with identity, endpoint, and network signals
- Investigate and respond using familiar tools and workflows
There’s no need to re-architect your environment or introduce new operational overhead. Hypervisor security becomes a seamless extension of your existing SecOps program running through a single pane of glass.
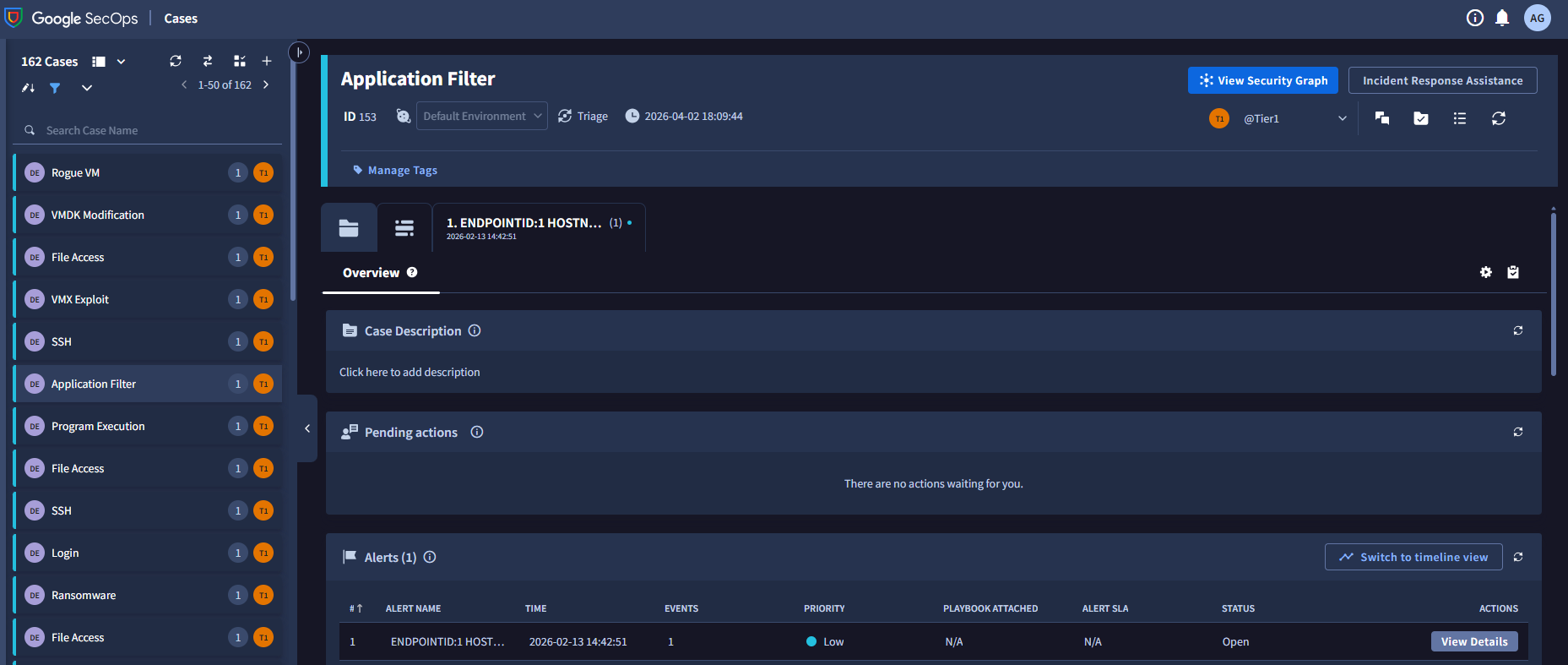
Figure 1: Hypervisor security events surfaced directly inside Google Security Operations.
Detect Earlier. Respond Faster.
By surfacing activity at the hypervisor layer, security teams can detect and investigate attacks earlier in the attack lifecycle—before they escalate across workloads.
This is especially critical as attackers increasingly target virtualization infrastructure to maximize impact and evade traditional controls.
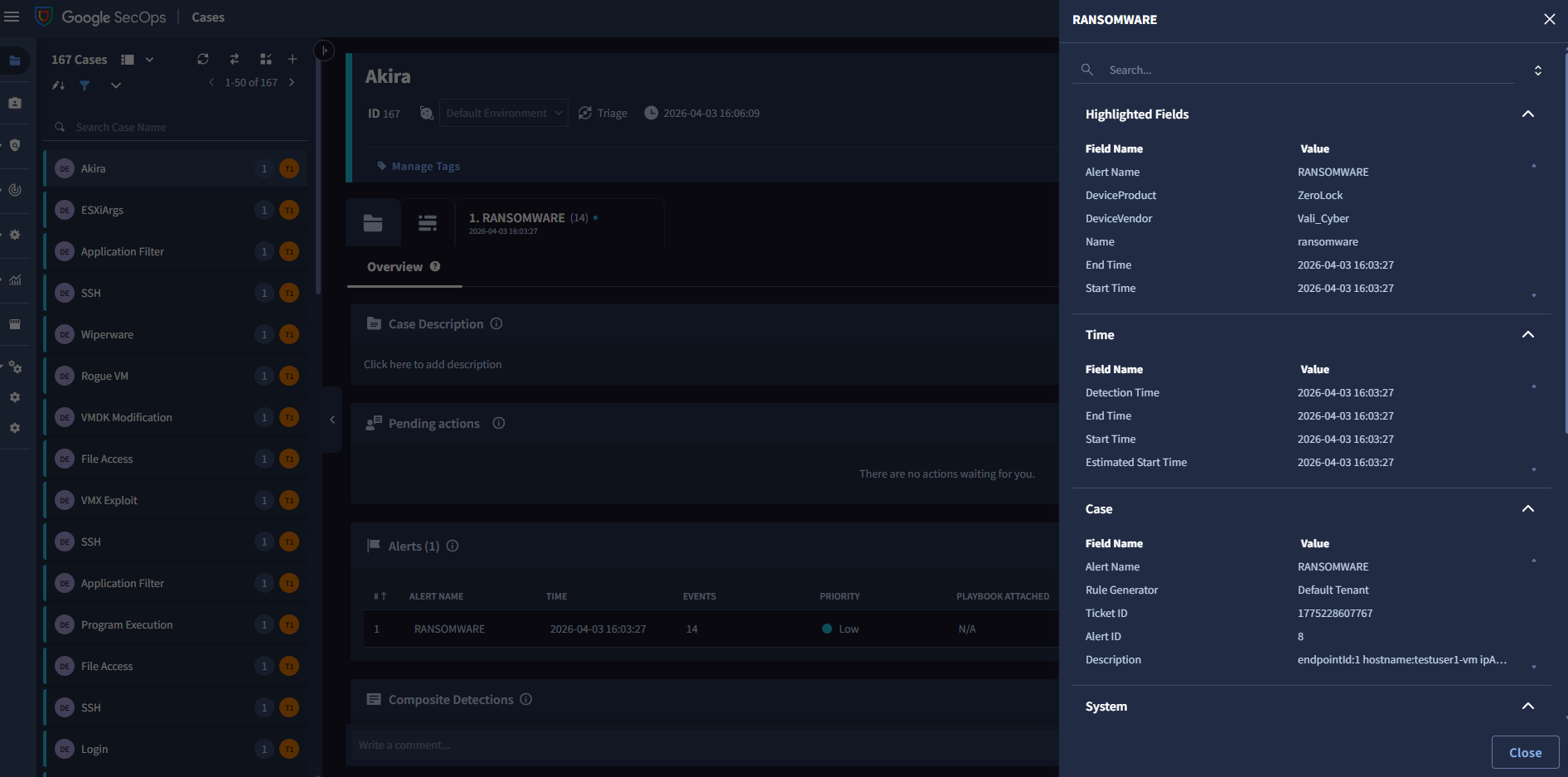
Figure 2: Hypervisor-level telemetry enabling earlier ransomware detection and investigation.
Built for Real-World Environments
The ZeroLock integration with Google Security Operations is:
- Production-ready and already deployed with customers
- Designed for easy adoption without disrupting existing architectures
- Aligned with how modern SecOps teams operate today
Interested? Learn more.
If you’re interested in learning more about ZeroLock and preemptive hypervisor security email [email protected].
How To Reduce Cyber Risk Before It Becomes Business Impact

When Ransomware ‘Brands’ Disappear, Their Tactics Don’t

As Workloads Move Back On-Prem, Hypervisors Emerge as a Quiet Mid-Market Risk

Hypervisor Ransomware: The Hidden Board-Level Attack Vector
Tech Scenes Unplugged Podcast
What Executives Need To Know About Threats Like Scattered Spider—And How To Avoid The Next Costly Breach

Vali Cyber Secures Growth Round to Meet Rising Demand for Hypervisor Ransomware Protection Amid Rising Attacks

How Virtual Patching Helps Protect Hypervisors Against Exploits

Hypervisor Ransomware: Why The C-Suite Can’t Ignore MITRE ATT&CK V17
Lock All The Doors: The Cybersecurity Risks Of Overlooked Devices In Computer Networks

20 Cybersecurity Response Scenarios Tech Teams Must Be Ready For

20 Tech-Related Threats We Must Not Ignore (And Solutions)

Operational Benefits Of Virtual Patching

