THE FIRST EVER RUNTIME SECURITY FOR HYPERVISORS
With recent attacks occurring due to compromised hypervisors, creating effective protection for Virtual Machine Monitors (VMMs) was a priority for us. We’re proud to introduce ZeroLock for Hypervisors. ZeroLock for Hypervisors is currently available for ESXi, Proxmox, Nutanix, XenServer, Citrix Hypervisor, Red Hat Enterprise Virtualization (RHEV), and KVM; contact us to learn more.
GET UP AND RUNNING FAST WITH ONE-LINE DEPLOYMENT.
ZeroLock is the first-ever runtime comprehensive security solution for all Linux-based Virtual Machine Monitors (VMMs). No modification to the hypervisor itself is required, and deployment is as simple as one line in the terminal. In addition to hypervisor protection, ZeroLock works across all Linux distros—with no need for kernel modules—while maintaining system stability, performance, and using only 50MB of RAM. Whether connected or disconnected, ZeroLock offers the same protection for:
-
Hypervisors (VMWare ESXi, Nutanix, XenServer, Citrix Hypervisor, Proxmox,
Red Hat Enterprise Virtualization (RHEV), and KVM) -
Private, Public, or Hybrid Cloud (Bare Metal/VMs, Containers, Kubernetes)
-
On-prem / Private Data Center
-
Embedded Systems and Controllers
-
Air-gapped Environments
ENSURE UPTIME WITH AI AND AUTOMATED FILE ROLLBACK.
ZeroLock’s patent-pending AI/ML-based behavioral capability detects malware by the actions it performs, not scanning for easily defeated file hashes. Our proprietary algorithms detect and stop traditional and fileless attacks in real-time with >98% efficacy and offer the ability to automatically remediate file damage with no user intervention required—helping you to ensure zero downtime.
- Ransomware Protection
- Wiperware Protection
- Cryptojacking Protection
- Automated Attacker Persistence Removal
- Real-time Threat Remediation
- Automated file rollback
- Fully Automated Process Tree Creation
PREVENT ATTACKS WITH REAL-TIME VIRTUAL PATCHING.
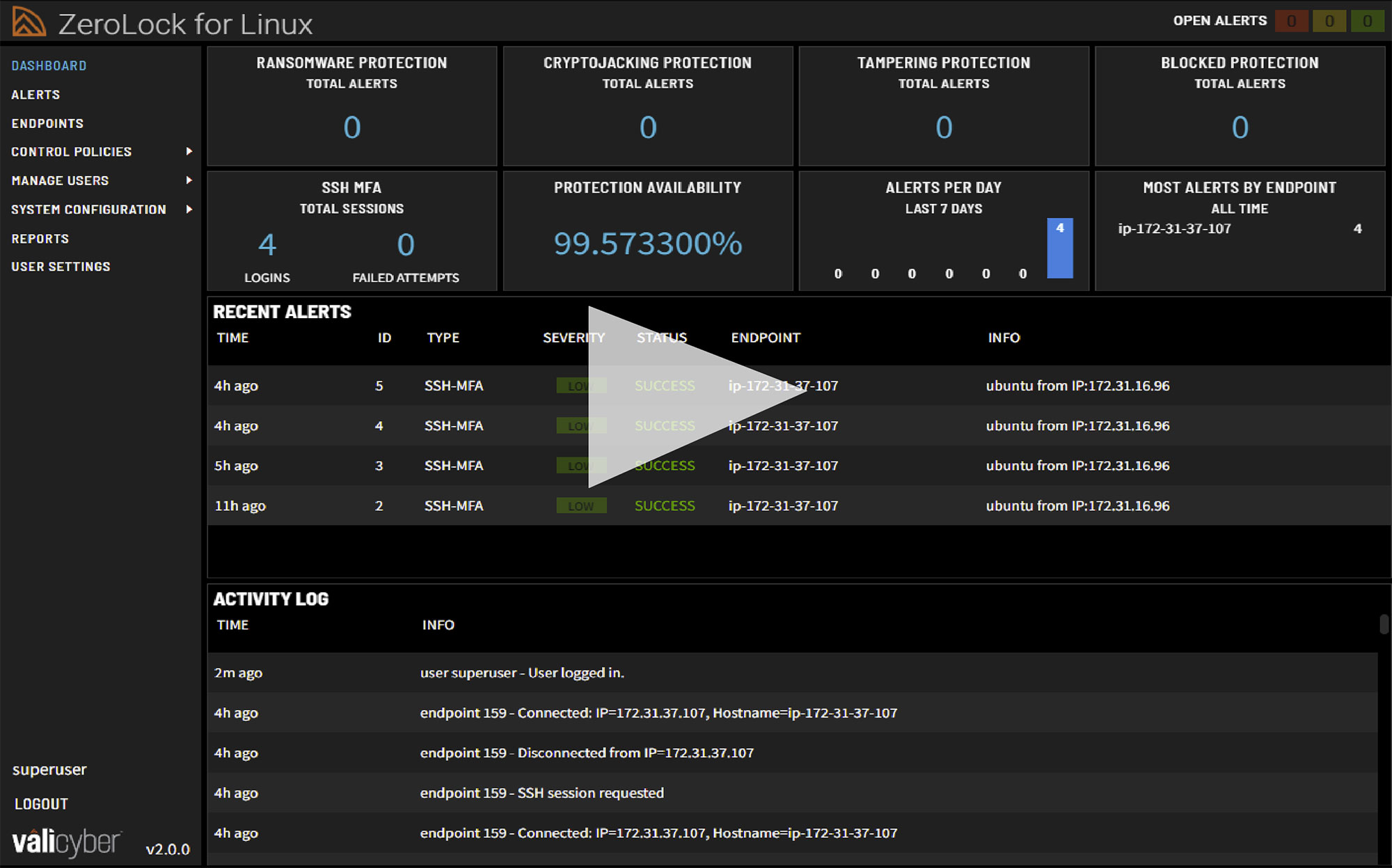
ZeroLock goes beyond traditional mandatory access control capabilities. In contrast to SELinux and AppArmor, ZeroLock offers easily configured and universally applied rules and policies that can be deployed across all your Linux and cloud environments from a single console. Examples of our control capabilities include:
- SSH Multifactor Authentication (MFA)
- Process Behavior Controls
- Network Access Controls
- File Access Controls
- Canary Files
- Tamper Protection
API-FIRST ARCHITECTURE FOR SIEM/SOAR INTEGRATIONS.
For teams that have existing platforms in place that they don’t want to disrupt—for their Windows endpoints for instance—ZeroLock has an API-first architecture with SIEM/SOAR integration capabilities to work into your environment, so you can have the best Linux security without sacrificing ease of management.
24-7 SUPPORT, EVERY STEP OF THE WAY.
TECH SPECS
ZeroLock® Endpoint Agent Requirements for Hypervisors
OS
• ESXi, 6.7+ (Older versions supported upon request.)
• Nutanix, AHV-2017+
• XenServer, 6.5+
• Citrix Hypervisor, 8.0+
• Proxmox, 3.0+
• Red Hat Enterprise Virtualization (RHEV), 3.6+
• KVM, Kernel 3.5+
Processor
x86-64, ARM-64 (coming soon)
Memory
50MB
Disk Space
100MB
Kernel Mods.
No kernel modification or modules required
Installation Methods
- One-line, web-based deployment (Wget)
- Filed-based deploy (Tar.gz or Bash)
- vSphere Lifecycle Manager and signed VIB for ESXi
RAM
8GB
Disk Space
100GB (dependent on number of endpoints and data retention duration)
CPU Cores
4 or more recommended
Installation Reqs.
Latest version of Docker installed.
Documentation
Visit api.zerolock.com for a full API.
Existing integrations
- SEIM: Splunk
- SOAR: Swimlane
CONTACT US
"*" indicates required fields