HYPERVISOR NEWS

Gartner Identifies the Top Strategic Technology Trends for 2026
“Technology leaders face a pivotal year in 2026, where disruption, innovation, and risk are expanding at unprecedented speed,” said Gene Alvarez, Distinguished VP Analyst at Gartner. “The top strategic technology trends identified for...
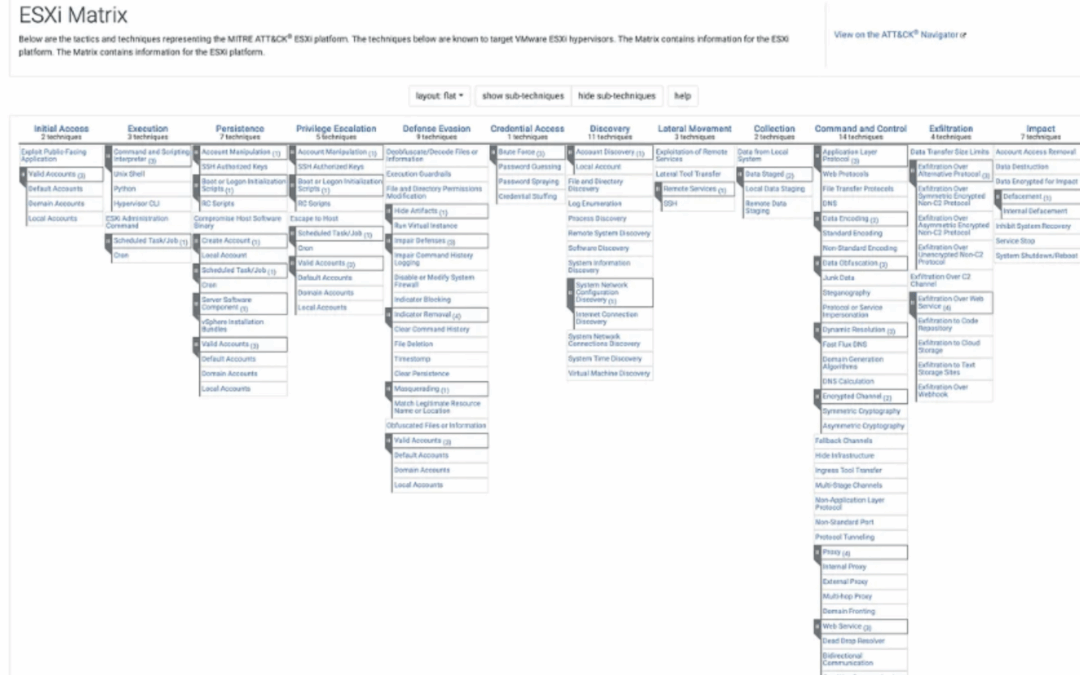
ATT&CK v17: New Platform (ESXi), Collection Optimization, & More Countermeasures
Our goal with ATT&CK v17 is to help defenders stay aligned with where adversaries are headed by looking at where they’ve recently been. This release aims to inform defensive efforts by focusing on the platforms adversaries are...

Threat Brief: VMware Vulnerabilities Exploited in the Wild (CVE-2022-22954 and Others)
On April 6, 2022, VMware published a security advisory mentioning eight vulnerabilities, including CVE-2022-22954 and CVE-2022-22960 impacting their products VMware Workspace ONE Access, Identity Manager and vRealize Automation. On April...

Global Incident Response Report 2025
We see five major emerging trends reshaping the threat landscape. First, threat actors are augmenting traditional ransomware and extortion with attacks designed to intentionally disrupt operations. In 2024, 86% of incidents that Unit 42...

Scattered Spider Hijacks VMware ESXi to Deploy Ransomware on Critical U.S. Infrastructure
The notorious cybercrime group known as Scattered Spider is targeting VMware ESXi hypervisors in attacks targeting retail, airline, and transportation sectors in North America. "The group's core tactics have remained consistent and do not...

Beyond Convenience: Exposing the Risks of VMware vSphere Active Directory Integration
Broadcom's VMware vSphere product continues to be a top choice for private cloud virtualization, underpinning important systems and critical infrastructure. Far from losing its appeal, organizations still rely heavily on vSphere for its...

Hypervisor Hangover: Persistence Mechanisms on ESXi
As FIN groups continue to execute fast-impact ransomware campaigns and nation-state APTs favor long-term infrastructure control, hypervisors have become the new high ground. This talk explores a set of stealthy, reliable persistence...

The 99% Solution: MFA for Hypervisor Security
Hypervisor attacks are accelerating, and the cost is catastrophic. Recent ESXi ransomware attacks have cost organizations hundreds of millions in recovery. In some cases, a single ESXi breach has led to costs exceeding $400 million. ...

RansomHub Is Gone—But Their ESXi Ransomware Tactics Still Threaten Virtual Infrastructure
In 2024, one ransomware group surged to the forefront: RansomHub. Rapidly dominating the ransomware-as-a-service (RaaS) landscape, this formidable cybercriminal network successfully breached over 600 organizations worldwide, targeting...

Hypervisor Ransomware: Why The C-Suite Can’t Ignore MITRE ATT&CK V17
Forbes.com
Virtual Demo: Scattered Spider Exposed How Hypervisor Attacks Really Work
Understand how ransomware groups like Scattered Spider compromise your virtual infrastructure—and how to stop them. In today's threat landscape, ransomware groups like Scattered Spider are increasingly targeting hypervisors, leading to...
Virtual Presentation: Protect Your Hypervisor from Ransomware
Attacks on hypervisors are increasing due to their devastating blast radius, as highlighted by the recent attacks on MGM Casinos, Johnson Controls, and MITRE. Now, you can protect your hypervisors: Vali Cyber offers the world’s only...

Scattered Spider: The Group Behind Major ESXi Ransomware Attacks
A new wave of ransomware actors is rewriting the rulebook. Their sights are set on VMware ESXi. Scattered Spider (AKA UNC3944, 0ktapus, Muddled Libra) is one of the most agile and dangerous threat clusters in operation today. They’re not...
From Retail Floors to Virtual Cores: ESXi Is the Next Attack Vector in Retail
In April 2025, Marks & Spencer—one of Britain’s most successful retailers—was crippled by a ransomware attack that didn’t just encrypt endpoints. It locked down VMware ESXi hypervisors, freezing core systems and bringing operations to...
Virtual Demo: A Hole in the Firewall – Why Network Defenses Just Don’t Cut It
Nathan Montierth and Joseph Comps from Vali Cyber's Threat Intelligence Team break down why traditional network defenses, such as firewalls, aren't enough to stop modern threats. Using a real-world inspired attack from UNC3886, where the...

Webinar: ATT&CK v17 Decoded: What IT & Security Teams Must Know
Exploits targeting hypervisors are at an all-time high. Enterprise virtualization is a prime target for threat groups due to valuable data and the challenges associated with preventing escape to host attacks. This has been validated with...
