As ransomware and advanced persistent threats continue to evolve, security teams are facing new security risks tied to the virtualization layer. VMware ESX hypervisors—responsible for running enterprise virtual machines (VMs) and managing the host operating system—have become a preferred target for modern threat actors.
Traditional VPNs and workload‑only Zero Trust models fail to address many of today’s most dangerous attack vectors, leaving gaps in virtualization layer security. Organizations must rethink their security strategy and extend Zero Trust Network Access (ZTNA) into the hypervisor itself using hypervisor runtime protection and preemptive security controls.
What Is Zero Trust Network Access (ZTNA)?
Think of Zero Trust like security in a modern office building. Instead of giving someone a master badge that lets them roam everywhere once they enter, every door checks who they are, whether they’re allowed in, and why they need access—every time.
Essentially, Zero Trust Network Access (ZTNA) is a defense‑in‑depth cybersecurity approach that enforces strict identity verification and least‑privilege access for every session. Unlike VPNs—which expose internal network traffic after login—ZTNA treats every request as untrusted.
Key ZTNA principles include:
- Identity‑based access enforcement
- Context‑aware authorization
- Continuous monitoring of sessions
- Reduction of lateral movement across virtual environments
However, most ZTNA deployments stop at the application layer, leaving gaps in virtualization layer security and hypervisor exploit prevention.
Why ESX Hypervisors Are a Growing Real‑World Target
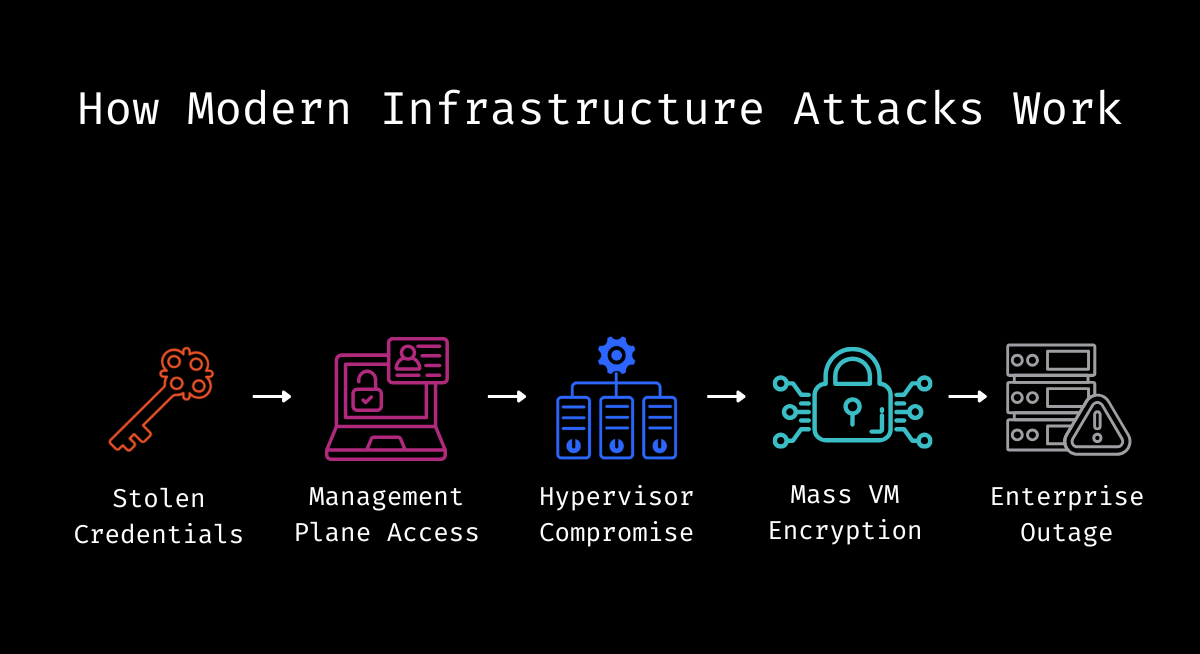
Attackers increasingly bypass endpoints and go straight for hypervisors. By exploiting hypervisor vulnerabilities, a threat actor can gain privileged access to multiple virtual machines, the underlying virtual network, and the sensitive data they process.
From ESXi ransomware to espionage campaigns, attackers abuse legitimate management paths, trusted open-source utilities, and administrative interfaces to avoid traditional detection systems. Once compromised, ESX becomes a force multiplier—turning a single intrusion into a widespread incident that complicates incident response and recovery.
This is why virtualization security best practices and ESXi security must evolve beyond detection and focus on runtime control.
Why VPNs and Workload‑Only Zero Trust Fail for ESX
Credential compromise has become routine—and attacker playbooks have evolved accordingly. Modern threat actors don’t break in; they log in. The numbers tell the story:
- 16 billion credentials exposed in 2025—fresh data, not recycled from old breaches
- 53% of breaches trace back to credential abuse—the #1 attack vector
- 292 days average dwell time, because attackers look legitimate
VPNs and application‑centric Zero Trust solutions focus on who can access the environment—not on what happens after access is granted. These controls stop at the workload or network layer and do not govern the ESX management plane, which is responsible for VM execution, storage, snapshots, and virtual networking. Once inside, attackers operating through stolen credentials or trusted admin tooling can manipulate the host OS, encrypt virtual machines, and exfiltrate data without triggering traditional controls.
In practice, this leaves critical gaps:
- Privileged ESX operations proceed without hypervisor level MFA
- Hypervisor processes and tools lack runtime enforcement
- Security relies on detection after compromise instead of prevention during execution
- Little visibility exists into abnormal behavior inside the hypervisor itself
Protecting ESX requires shifting Zero Trust beyond access decisions and into runtime enforcement at the hypervisor layer.
Extending Zero Trust with Hypervisor Runtime Protection
Hypervisor runtime protection enforces identity‑ and behavior‑based controls during execution, enabling organizations to stop attacks as they happen rather than relying on detection after compromise.
Key capabilities include:
- Hypervisor exploit prevention and zero‑day protection for hypervisors
- Virtual patching for hypervisors without downtime
- Application control for hypervisors and runtime anomaly detection
- Preemptive security controls that reduce blast radius and dwell time
ZeroLock hypervisor protection applies these principles directly inside ESX. With ZeroLock runtime security, security teams gain visibility and control over hypervisor activity in real time—before ransomware encryption, VM disruption, or data loss occurs.
The Takeaway for Security Teams
A modern ESX security strategy requires more than workload protection. This means:
- Treating the hypervisor as a first‑class security boundary
- Extending Zero Trust to include runtime enforcement, not just identity checks
- Adopting a hypervisor security solution that protect the virtualization layer itself
As attackers continue to target virtualization, organizations that rely only on access‑based controls will remain exposed. Protecting ESX means protecting the layer everything else depends on—with a defense‑in‑depth cybersecurity platform that operates at runtime.
