Aliases
- Agenda (original name, 2022)
- Gold Feather (Secureworks)
- Water Galura (Trend Micro)
Get Threat Intel and Security Updates Delivered to Your Inbox.
Profiling
Threat Actor Type: Ransomware-as-a-Service (RaaS) with global affiliate network.
Origin: Believed to be a Russian-speaking criminal organization. The malware avoids targeting systems in Commonwealth of Independent States (CIS) countries — a common indicator of Russian-linked threat actors. Russian language was observed in underground forum posts used to recruit affiliates.
Structure: Core development team maintains the RaaS platform and tooling; a distributed network of affiliates conducts attacks and retains 80–85% of ransom payments, remitting 15–20% to Qilin leadership.
Expertise: Highly technically capable cross-platform ransomware operators. Qilin maintains dedicated encryptors for Windows, Linux, and VMware ESXi environments — with the ESXi encryptor purpose-built to shut down VMs, release VMDK file locks, delete snapshots, and encrypt virtual disk files.
- In 2025, Qilin introduced a novel technique of running Linux ELF encryptors inside Windows Subsystem for Linux (WSL) to bypass Windows-focused EDR tools.
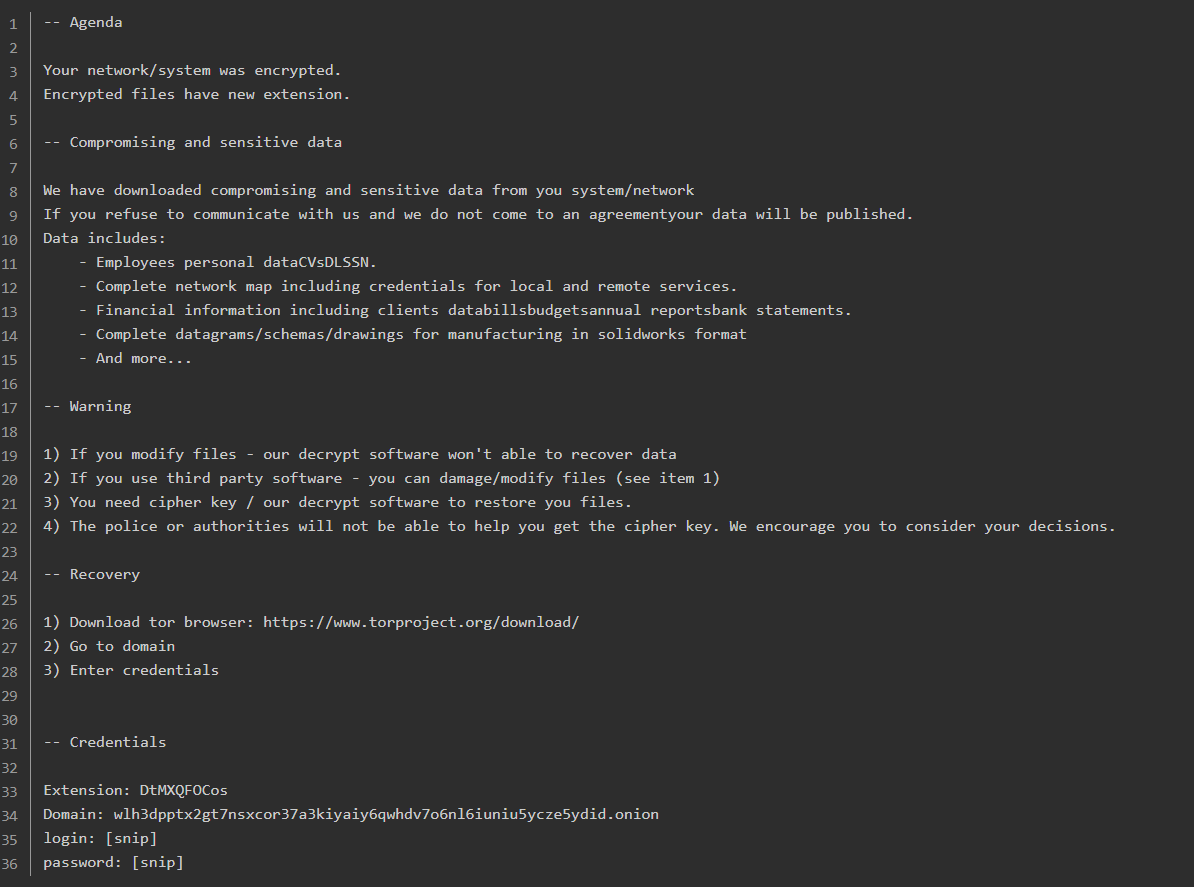
Qilin “Agenda” ransom note.
Motivations
Financial gain via ransomware encryption, data exfiltration, and extortion. Qilin does not discriminate by sector or organization size — victims range from multinational corporations to small municipal governments and non-profits.
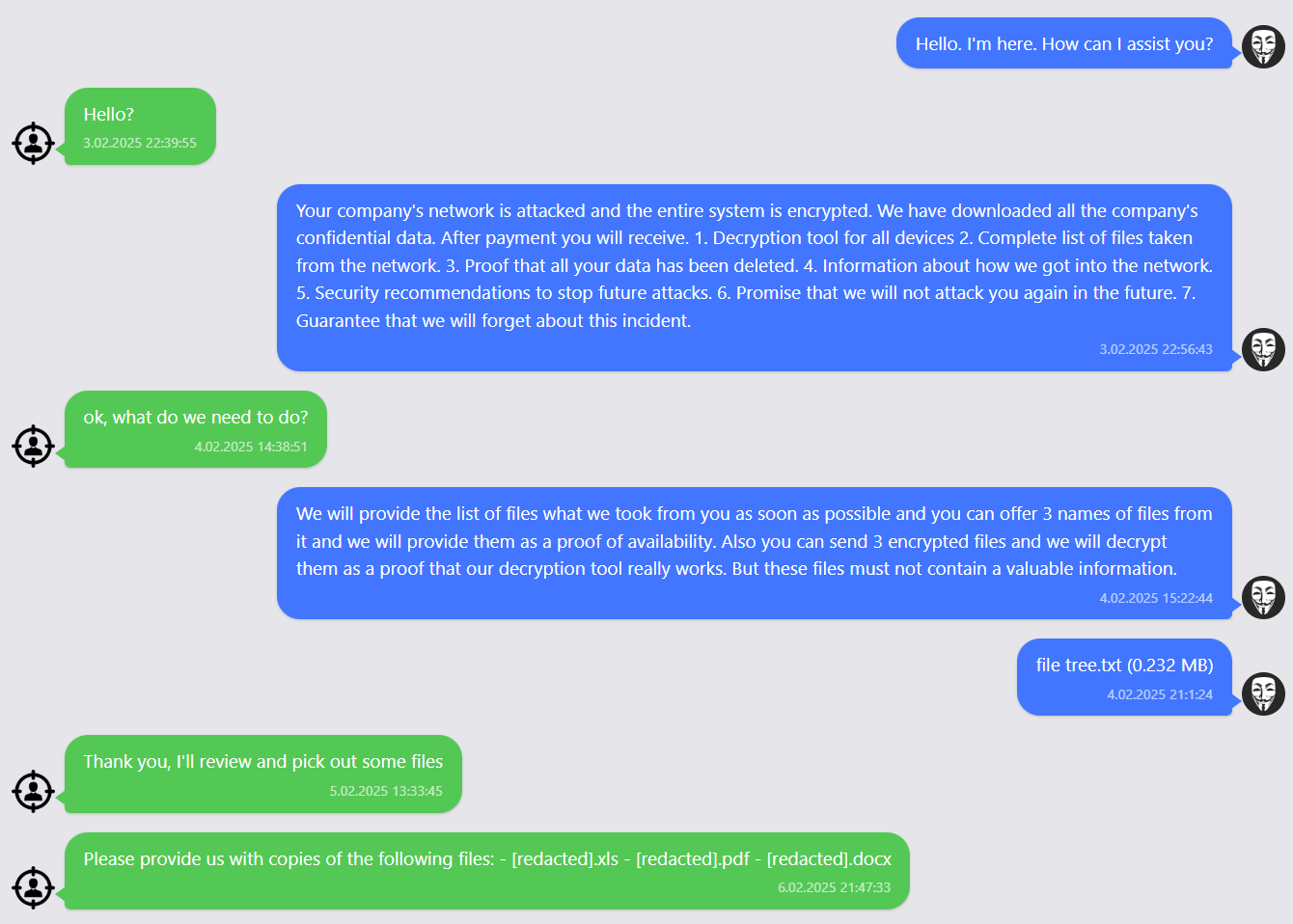
Negotiation chats with Qilin.
Timeline & Victimology
2022 – Emergence as “Agenda”
Ransomware first observed in July/August 2022 under the name “Agenda,” written in Go (Golang) and initially targeting Windows. Each sample was customized per victim, using unique company IDs as encrypted file extensions.
Late 2022 – Rebrand to Qilin
Group rebrands to “Qilin” (named after a Chinese mythological creature), posts first victim data on dedicated leak site. Codebase begins transition to Rust for improved cross-platform capability and evasion.
2023 – ESXi Targeting Emerges
Qilin introduces a purpose-built Linux/ESXi encryptor — one of the most customizable seen in the wild. Encryptor focuses specifically on VMware virtual machines: enumerating VMs, shutting them down, deleting snapshots, and encrypting VMDK files. Victim activity increases through late 2023.
2024 – Major Escalation & NHS Attack
- June 2024: Attacks Synnovis, a pathology services provider for NHS hospitals in London. Causes a “critical incident” — canceled surgeries, diverted emergency patients, blood transfusion shortages. UK officials later confirmed the disruption contributed to a patient’s death. 400 GB of data stolen and leaked.
- Introduces Chrome credential-stealer functionality to harvest browser-stored passwords.
- Amasses over $50 million in ransom payments for the year.
2025 – #1 Most Active Ransomware Group
- Surpasses RansomHub in Q2 2025 to become the most active ransomware operation globally.
- Executes 70 attacks in a single 30-day window (August–September 2025) spanning North America, Europe, Asia, Africa, and Latin America.
- Claims 792+ victims by September 2025; U.S. accounts for more than half (436 victims).
- DragonForce claims Qilin has joined their ransomware cartel alongside LockBit.
Current Status (2026) Qilin remains highly active with new victims posted to its DLS weekly. No major arrests or law enforcement operations have disrupted operations. The group continues to evolve its tooling, expand affiliate recruitment, and refine its ESXi-targeting capabilities.
Tactics & Techniques
Initial Access
- Phishing / Spearphishing (T1566) — including targeted campaigns against MSP administrators (e.g., ScreenConnect admin compromise leading to downstream customer attacks)
- Exploitation of public-facing applications (T1190) — notably FortiGate VPN vulnerabilities (CVE-2024-21762, CVE-2024-55591) and SAP NetWeaver Visual Composer (CVE-2025-31324, CVSS 10.0)
- External Remote Services / RDP abuse (T1133)
- Valid Accounts / stolen credentials (T1078)
Execution & Lateral Movement
- Cobalt Strike for post-exploitation and C2 (T1059)
- SmokeLoader and NETXLOADER (.NET compiled loader) for payload staging
- PsExec, NetExec, WinRM, WMI for lateral movement (T1021)
- RDP-based lateral movement (T1021.001)
- VMware vCenter abused for self-distribution across virtualized environments
Defense Evasion
- Bring Your Own Vulnerable Driver (BYOVD) to disable endpoint security (T1068)
- WSL (Windows Subsystem for Linux) used to run Linux ELF encryptors on Windows hosts, bypassing Windows-only EDR (T1202)
- Safe Mode reboots to bypass endpoint defenses (T1562)
- Log tampering to remove forensic evidence (T1070)
Credential Access
- Chrome credential stealer targeting browser-stored passwords (T1555.003)
- Veeam backup credential theft (T1078)
- Credential dumping (T1003)
Impact
- Data Encrypted for Impact — Windows, Linux, and VMware ESXi environments (T1486)
- VMware ESXi specific: VM shutdown → snapshot deletion → VMDK encryption
- Inhibit System Recovery — Volume Shadow Copy deletion via vssadmin.exe (T1490), backup job disabling, tape backup deletion
- Data exfiltration via WinRAR + easyupload[.]io and rclone for double extortion (T1041)
Defensive Recommendations Against Qilin
Defending against Qilin requires layered controls across identity, network, backup infrastructure, and the hypervisor itself:
Identity and Access Hardening: Enforce phishing-resistant MFA across remote access tools, VPNs, and admin portals. Apply least privilege and monitor for credential abuse, especially against backup platforms like Veeam.
Patch Management: Prioritize patching of internet-facing appliances. Qilin affiliates actively exploit FortiGate VPN vulnerabilities and zero-day flaws in enterprise software (SAP NetWeaver). Rapid patching significantly reduces initial access opportunities.
MSP and Supply Chain Vigilance: Qilin has demonstrated consistent ability to breach MSPs and propagate ransomware to downstream customers. MSPs should enforce strict segmentation between customer environments and monitor admin tooling (e.g., ScreenConnect, Splashtop) for anomalous use.
Backup Integrity: Maintain offline, segmented backups. Qilin affiliates specifically target Veeam backup infrastructure to steal credentials and destroy recovery options before deploying encryption. Backups accessible from the network are at risk.
Hypervisor-Layer Defense: Qilin’s dedicated ESXi encryptor — and its ability to route Linux encryption through WSL on Windows hosts — makes hypervisor-layer defenses essential. Standard EDR tools operating at the Windows PE level are insufficient against these techniques.
References
AttackIQ. Emulating the Versatile Qilin Ransomware. https://www.attackiq.com/2025/10/02/emulating-qilin-ransomware/
Blackpanda. Case Study: Qilin Ransomware Cripples ESXi. https://www.blackpanda.com/case-studies/qilin-ransomware-esxi-incident-response
Center for Internet Security. Qilin: Top Ransomware Threat to SLTTs in Q2 2025. https://www.cisecurity.org/insights/blog/qilin-top-ransomware-threat-to-sltts-in-q2-2025
Darktrace. A Busy Agenda: Darktrace’s Detection of Qilin Ransomware. https://www.darktrace.com/blog/a-busy-agenda-darktraces-detection-of-qilin-ransomware-as-a-service-operator
MITRE ATT&CK. Qilin, Software S1242. https://attack.mitre.org/software/S1242/
Qualys. Qilin Ransomware Explained: Threats, Risks, Defenses. https://blog.qualys.com/vulnerabilities-threat-research/2025/06/18/qilin-ransomware-explained-threats-risks-defenses
Ransomware.live. Qilin. https://www.ransomware.live/group/qilin
Trend Micro. Agenda Ransomware Propagates to vCenters and ESXi via Custom PowerShell Script. https://www.trendmicro.com/en_us/research/24/c/agenda-ransomware-propagates-to-vcenters-and-esxi-via-custom-pow.html
