Aliases
- Dark Angels
- Dark Angels Team
- White Rabbit
Related Historical Identifiers
- MARIO (ESXi) – Babuk-derived ESXi encryptor assessed as part of the Dark Angels lineage
- Dunghill – data leak and extortion site branding used in Dark Angels campaign
Get Threat Intel and Security Updates Delivered to Your Inbox.
Profiling
Threat Actor Type:
- Financially motivated ransomware and data extortion group specializing in high-value, low-volume intrusions. Dark Angels prioritizes large enterprises, focusing on data theft first and selective encryption (often at the hypervisor / ESXi layer) to maximize leverage while minimizing operational noise.
Communications & Infrastructure:
- Uses Tor-based leak sites and Telegram channels (notably @leaksdirectory) to pressure victims and publish stolen data.
- Does not operate as a traditional RaaS affiliate model; campaigns are tightly controlled and highly targeted.
- Ransom negotiations are conducted privately, often resulting in non-publicized payments.
Expertise:
- Windows and Linux/VMware ESXi ransomware payloads
- Largescale data exfiltration (TBs) prior to encryption
- Privilege escalation to domain and hypervisor admin
- Long dwell intrusions with extensive reconnaissance
- Custom tooling derived from Babuk (Windows) and RagnarLockerlike codebases (Linux/ESXi)
Motivations
Primary:
- High value extortion through double extortion (data theft + selective encryption), often demanding tens of millions of dollars.
Public reporting confirms Dark Angels received a $75M ransom payment in 2024, the largest publicly known ransomware payment to date, from an unnamed Fortune level organization.
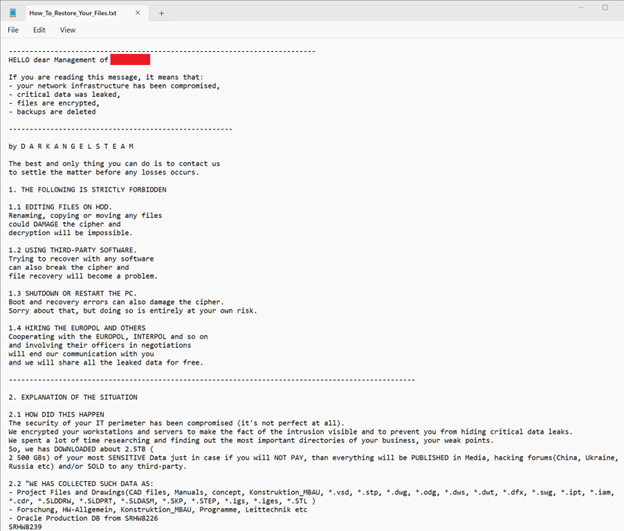
Figure 1: Dark Angels ransom note.
Timeline & Victimology
2021–Early 2022 – Formation
- Group claims inception in 2021; first confirmed activity observed in April 2022.
- Early tooling strongly linked to leaked Babuk ransomware source code.
2022–2023 – Targeted Enterprise Intrusions
- Shift toward “big game hunting”: fewer victims, higher ransom demands.
- Focus on manufacturing, healthcare, technology, and industrial sectors across North America, Europe, and Asia.
September 2023 – ESXi-Focused Attack (Johnson Controls)
- Dark Angels compromises VMware ESXi hosts, encrypts virtual machines, and exfiltrates ~27 TB of corporate data.
- Reported ransom demand exceeded $50M.
2024 – Record Breaking Ransom
- Security researchers and crypto intelligence firms confirm a $75M ransom payment to Dark Angels, marking the largest known ransomware extortion payment publicly disclosed.
2024–2025 – Mature ESXi & Linux Operations
- Discovery of bespoke Linux/ESXi encryptors, distinct from Babuk, optimized for:
- Datastore enumeration
- VM encryption
- Snapshot disruption
- Continued preference for stealth, persistence, and data theft over mass encryption.
Tactics & Techniques
Initial Access
- Phishing / Spearphishing — T1566
- Exploit Public Facing Application — T1190
- Valid Accounts — T1078
- Exploitation of Known Vulnerabilities (e.g., CVE202322069) — T1190
Execution
- Command and Scripting Interpreter — T1059
- Service Execution — T1569.002
Persistence & Privilege Escalation
- Account Manipulation — T1098
- Abuse Elevation Control Mechanism — T1548
Defense Evasion
- Impair Defenses — T1562.001
- Clear Event Logs — T1070.001
Credential Access
- Credential Dumping — T1003
- Account Discovery — T1087
Lateral Movement
- Remote Services — T1021
- SMB / Admin Shares — T1021.002
Collection & Exfiltration
- Automated Collection — T1119
- Archive Collected Data — T1560
- Exfiltration Over Web Services — T1567.002
Impact
- Data Encrypted for Impact — T1486
Defensive Recommendations Against Dark Angels
- Treat VMware ESX and the hypervisor as a primary attack surface, not just infrastructure.
- Restrict and monitor ESX administrative access, including ADintegrated permissions.
- Monitor for snapshot deletion, datastore encryption, and unusual VM operations.
- Detect longdwell lateral movement and reconnaissance, not just ransomware deployment.
- Maintain offline, immutable backups of VM images and critical data.
- Prioritize preencryption detection (data exfiltration, privilege escalation, ESXi command execution).
References
Zscaler ThreatLabz. Shining Light on the Dark Angels Ransomware Group. https://www.zscaler.com/blogs/security-research/shining-light-dark-angels-ransomware-group
Daily Security Review. Dark Angels Ransomware: Sophistication & HighStakes Attacks. https://dailysecurityreview.com/resources/dark-angels-ransomware-sophistication-high-stakes-attacks/
Cybersecurity Insiders. Johnson Controls Hit by Dark Angels Ransomware. https://www.cybersecurity-insiders.com/johnson-controls-hit-by-dark-angels-ransomware/
ISACA. DarkAngels Strikes Big: RecordBreaking Ransom Secured. https://www.isaca.org/resources/news-and-trends/industry-news/2024/darkangels-strikes-big-record-breaking-ransom-secured
