Aliases
- DarkBit Ransomware
- esxi.darkbit (Linux/ESXi payload name observed in incident response)
Get Threat Intel and Security Updates Delivered to Your Inbox.
Profiling
Threat Actor Type:
- Ransomware operation assessed to function as a politically motivated disruption tool rather than a purely financially driven Ransomware as a Service (RaaS) group.
Suspected Attribution:
- Multiple independent sources link DarkBit activity to the Irannexus threat actor MuddyWater, an APT group historically associated with cyberespionage and sabotage campaigns.
Expertise:
- Purpose built ransomware targeting VMware ESXi environments
- Strong operational knowledge of hypervisor administration and VMFS datastores
- Focus on rapid service disruption rather than prolonged negotiations
- Limited evidence of iterative ransomware development or affiliate ecosystems
Communications & Infrastructure:
- Ransom notes containing political messaging and fixed payment demands
- No long running public leak site or sustained victim-shaming infrastructure
- Campaigns show minimal engagement with victims post-encryption
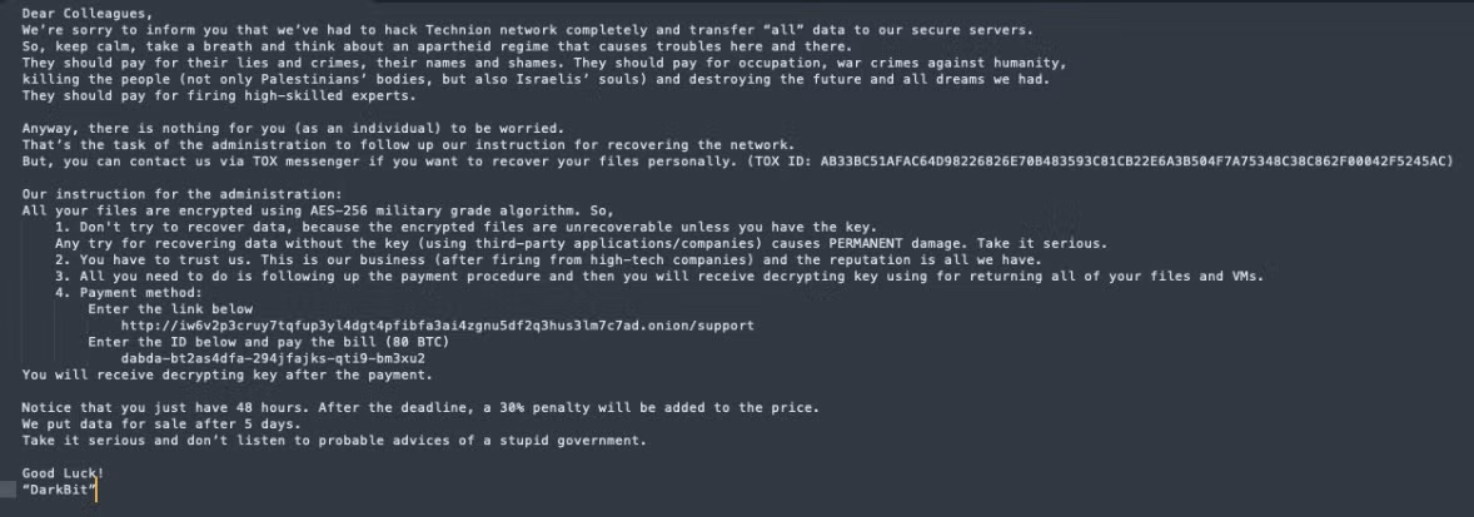
DarkBit ransom note.
Motivation
Primary Motivation: Operational disruption aligned with geopolitical objectives, rather than consistent revenue generation.
Secondary Motivations:
- Psychological and reputational impact
- Signaling capability following regional political or military events
- Use of ransomware tooling as a cover for state aligned sabotage activity
Timeline
2023 – Initial Activity Observed
- DarkBit campaigns detected following regional geopolitical events.
- Attacks encrypting multiple VMware ESXi servers within a single organization were investigated by incident response teams.
2025 – Technical Disclosure & Cryptographic Break
- Security researchers disclosed critical flaws in DarkBit’s encryption implementation.
- Victims were able to recover data without paying ransom due to predictable key generation and partial encryption of VMDK files.
Current Status (as of March 2026)
- No evidence of an active mass scale campaign or modernized variants.
- DarkBit remains relevant as a case study in hypervisor targeted, politically motivated ransomware, rather than a high-volume criminal operation.
Tactics & Techniques
Initial Access
Public reporting does not conclusively document a single initial access vector. Sources indicate compromise occurred prior to ESXi level execution. No zero-day exploitation has been publicly attributed.
Execution
- T1059.012 – Command and Scripting Interpreter: Hypervisor CLI: Abuses native ESXi utilities (e.g., esxcli) to stop virtual machines and prepare hosts for encryption.
Discovery
- T1083 – File and Directory Discovery: Enumerates VMFS datastores to locate virtual machine files.
- T1613 – Virtual Machine Discovery: Identifies running VMs prior to encryption.
Impact
- T1486 – Data Encrypted for Impact: Encrypts VMDK, VMX, and NVRAM files on ESXi hosts.
- T1529 – System Shutdown / Reboot: Stops virtual machines before encryption to ensure maximum disruption.
- T1490 – Inhibit System Recovery (partial): Hypervisor‑level encryption prevents VM recovery without backups.
Victimology
Victim Disclosure: No public leak site and has not reliably named victims in public channels.
Observed Victim Characteristics:
- Organizations with centralized VMware ESXi infrastructure
- Multidepartment enterprises
- Educational institutions
Geographic Focus: Israel (primary and repeatedly documented), surrounding regions
These patterns are consistent with politically motivated targeting rather than opportunistic ransomware victim selection.
Defensive Recommendations
- Restrict and monitor direct ESXi host access
- Audit and alert on ESXi command line usage (esxcli, VM shutdown activity)
- Enforce strict credential hygiene for hypervisor administrators
- Maintain offline, immutable backups of VM disk files
- Treat ransomware activity with political messaging as potential state aligned disruption, not standard extortion
References
Toulas, B. (2025, August 11). MuddyWater’s DarkBit ransomware cracked for free data recovery. BleepingComputer.
https://www.bleepingcomputer.com/news/security/muddywaters-darkbit-ransomware-cracked-for-free-data-recovery/
Paganini, P. (2025, August 12). Researchers cracked the encryption used by DarkBit ransomware. Security Affairs.
https://securityaffairs.com/181064/malware/researchers-cracked-the-encryption-used-by-darkbit-ransomware.html
Doyle, A. (2026, February 4). MuddyWater’s DarkBit ransomware cracked, allowing free data recovery. Daily Security Review.
https://dailysecurityreview.com/security-spotlight/muddywaters-darkbit-ransomware-cracked-allowing-free-data-recovery/
Cyber Security News. (2025, August 12). DarkBit hackers attacking VMware ESXi servers to deploy ransomware and encrypt VMDK files.
https://cybersecuritynews.com/darkbit-hackers-attacking-vmware-esxi-servers/
GBHackers. (2025, August 12). DarkBit hackers target VMware ESXi servers to deploy ransomware.
https://gbhackers.com/darkbit-hackers-target-vmware-esxi-servers/
Thailand Computer Emergency Response Team (ThaiCERT). (2025, August 15). DarkBit ransomware decrypted, allowing victims to recover data without paying ransom.
https://www.thaicert.or.th/en/2025/08/15/darkbit-ransomware-decrypted-allowing-victims-to-recover-data-without-paying-ransom/
