BLOG POSTS

BUILDING IN ROBUSTNESS FROM THE START (Part 1): A Critical Look at Resilient Software Development
By Austin Gadient Challenges in Keeping Software Clean and A New Hope The recent global outage caused by an update to the CrowdStrike Falcon agent caused me to reflect on software development and software design practices, with a focus on...
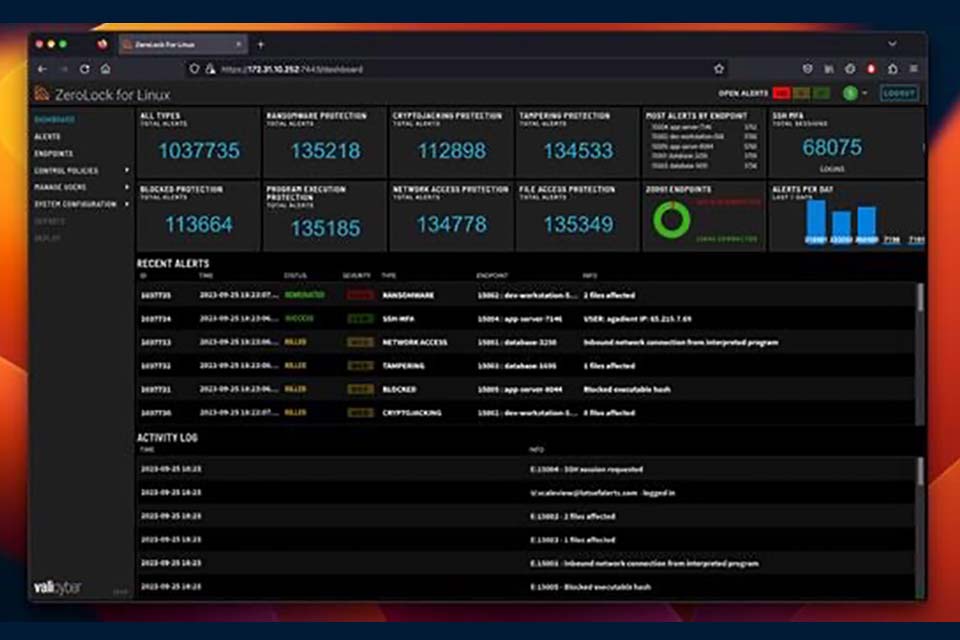
Vali Cyber® Announces Early Access to the First Ever Runtime Security Platform for ESXi
Vali Cyber, Inc., a next-generation provider of Linux cybersecurity solutions, announces that its autonomous zero-trust security platform, ZeroLock® has been expanded to protect ESXi hypervisors, 6.7+. With no other runtime security...

The Critical Role of Hypervisor Security in the Financial Sector
Imagine a financial institution where all virtual machines—responsible for everything from customer transactions to trade executions—suddenly go dark. As a result, operations freeze, data is locked, and millions are at stake. This is not...

The Urgent Need for Hypervisor Security in Healthcare
In this white paper, we examine the threats the healthcare sector faces, emphasizing the crucial need for enhanced cybersecurity measures.

Ransomware in the Education Sector
In recent years, educational institutions have been relentlessly targeted by cyber-attacks, with hypervisor vulnerabilities standing out as one of the most critical risks. As remote learning has proliferated, the IT landscape in academia...
Vali Cyber® Secures $15M in Seed Funding to Revolutionize Linux Cybersecurity
Vali Cyber, Inc., a next-generation provider of Linux cybersecurity solutions, announces the successful completion of its seed funding round, raising USD 15 million. The funding round was co-led by Grotech Ventures and the 412 Venture Fund (412VF) and aided with strong support from Riverfront Ventures, Florida Funders, and additional strategic investors.

AI Kills Hash Based Detections
Whether it is ChatGPT, GPT4, Bard, or any of the other AI systems competing for public attention, these systems represent a significant leap forward in Malware as a Service (MaaS) capabilities. While it is true there are supposed to be...
A Brief History of NAS Ransomware
It is no secret that NAS devices are frequently targeted by ransomware attacks, and for good reason. Critical data is often stored on devices. Furthermore, NAS devices typically store large amounts of data. NAS devices run Linux operating...
